If you visit a popular community like /c/memes@lemmy.ml with your web browser, the images shown are hotlinked from the Lemmy instance that the person posting the image utilized. This means that your browser makes a https request to that remote server, not your local instance, giving that server your IP address and web browser version string.
Assume that it is not difficult for someone to compile this data and build a profile of your browsing habits and patterns of image fetching - and is able to identify with high probability which comments and user account is being used on the remote instance (based on timestamp comparison).
For example, if you are a user on lemmy.ml browsing the local community memes, you see postings like these first two I see right now:
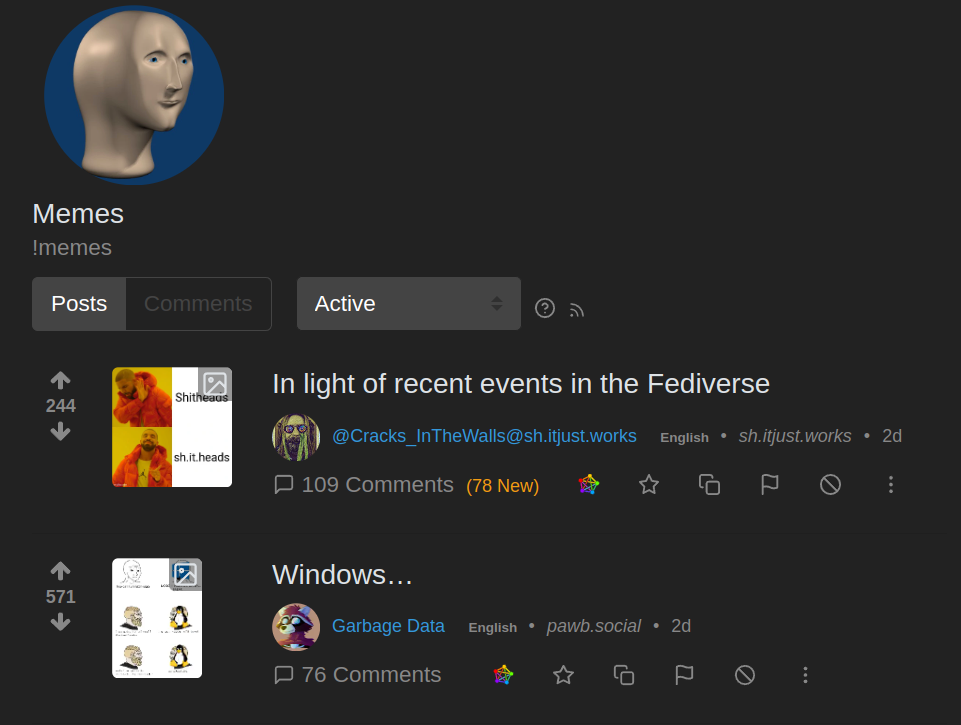
You can see that the 2nd one has a origin of pawb.social - and that thumbnail was loaded from a sever on that remote site:
https://pawb.social/pictrs/image/fc4389aa-bd4f-4406-bfd6-d97d41a3324e.webp?format=webp&thumbnail=256
Just browsing a list of memes you are giving out your IP address and browser string to dozens of Lemmy servers hosted by anonymous owner/operators.
deleted by creator
Have a basic firewall enabled.
This isn’t about a firewall. This is about some image hoster figuring out and keeping records of your usage times, location tracking, for your account that comments and posts.
Lemmy is at a point where typical new-user sign-up had no terms of service, privacy policy, cookie policy - people need to understand that this is not a hardened and mature platform. There could be a lot of things that people didn’t expect - that a major corporation like Reddit or Twitter would be scrutinized more closely over.
GDPR believes an IP address is a private information. This can be used to mount a legal attack on EU-hosted lemmy instances.
I’d imagine that applies to a website sharing or selling logs of user ips that visited, if you go hit some other server, you give them your ip so they can talk back to you. You’re basically doing this on almost every website because almost all will use third party cdns like fonts.google.com or others for Javascript libraries etc. If linking content from another site is the actual interpretation, the modern web basically can’t legally exist in the EU.
If IP address sharing via hotlinked images, embedded content, etc were breaking GDPR I think the entire internet is breaking it. If I visit a blog, and then click an embedded video or image on that page, then my IP has been shared to someone else while visiting that page. This occurs on the vast majority of the internet.
EDIT: It wouldn’t just be EU-hosted lemmy instances either. GDPR applies to servers outside of EU jurisdiction whenever they’re serving residents of the EU.
Indeed. Most of the web is broken under GDPR’s privacy requirements.
Is rhere anything end users can do about it, or is it a choice between using the fediverse or not using the fediverse?
At this point, raise awareness that it isn’t like a major identifiable social media site who has a reputation to worry about. Right now, anyone can create a Lemmy instance and join the federation, there is no approval or application process.
It’s a lemmy thing, kbin appears not to hotlink. and mastodon allso doesn’t hotlink.
I agree 100%, people need to know what they aare using and doing, especially less savvy or less curious users who wont seek out this kind of information on their own.
Im asking though, is their anything that can be done by the user themselves to obscure their IP when loading images, or is it just something that has to be accepted as part of using the fediverse if you want to use it, and thats just that.
Some people use VPN… and every day they are getting a different IP address when they connect to their VPN…
It’s normal, what’s ‘new’ to people is that the images are loaded from peer. Especially coming from Reddit (where it uses thumbs.redditmedia.com), that is different from what most people expect. They assume you have to click a link to go off-site. “hotlinking” the images as Lemmy is typically doing right now involves more parties.
The Mullvad Browser. Think of it like the Tor Browser without Tor. That combined with Mullvad’s VPN service would address both of the legitimate issues brought up in the OP.
Now that is purely passive, just data collection from routine serving of images.
A rogue site could start serving crafted images to confuse users or cause NSFW content to appear on all other Lemmy sites where users were browsing a meme.
When you have small-time image hosts being used by the dozens, they likely aren’t as worried about their reputation being burned by pranks like this.
This applies to any website. by visiting the website you give them your IP. the only way to mitigate this is to use a VPN.
I know very little about networks, but aren’t end-users IP addresses dynamically assigned by their Internet providers? Don’t providers use NAT systems so the public IP you see is not actually the one assigned to someone’s “house”?
Don’t providers use NAT systems so the public IP you see is not actually the one assigned to someone’s “house”?
Typically NAT ends at the building. So a coffee shop it is going to use private addresses for every person on WiFi inside the coffee shop, but the servers are still going to get the single IP address of that building.
You can see what a typical database might say about your IP address: https://www.iplocation.net/ and compare with another service: https://iplocation.com/
Thanks, iplocation.net has a lot more detail than iplocation.com, but they both show exactly the same public IP for me (that is my provider), were they supposed to be different on the 2 sites?
hey both show exactly the same public IP
Your Public IP won’t change, but the different databases guessing where that is, interpretation changes.
It was coincidence that they had similar names, I went through the first 5 ot 6 I found on a Google Search and picked two that had different actual information.
With the same IP, the first site thinks I am 2 states away in the USA (1300 miles wrong), the 2nd site shows exactly where I am. Almost all the sites show me 2 states away, but iplocation.com must have had someone identify the hotel I am at.
Oh I see, in my case both show the same location, probably because I’m at home and what they show is my internet provider, it’s probably easy to know exactly where providers actually are.
Big instances surfing up content from smaller instances is invariably going to cripple them unless larger instances start locally caching that content.
A “solution” to this might be for lemmy instances/apps to have the option to “load remote images” the way e-mail providers do. So I have to actively click to load the images. Could even be done per subscription, so I could declare that I just want everything loaded when I see lemmy.ml/c/pics but not in general, where I usually want text.
IP Address isn’t extremely precise, and I always run on the latest version of whatever browser I’m on, be it Safari or Edge.
Ever heard of a VPN?
If you use a VPN, the analysis of timestamp probability in logs is still going to reveal that you are likely the user who made x comment at y time. Another lemmy instance you never signed up at can start to look in logs for your comment id: #734995 and cross-reference it to image loading.
This can happen with literally any web host. It’s not something exclusive to Lemmy, I’m not sure why you’re acting like it is?








